These are the steps for a simple DNS migration to AWS Route 53.
For our convenience, we have previously migrated our Internet Domain registration to Route 53 using these instructions (optional).
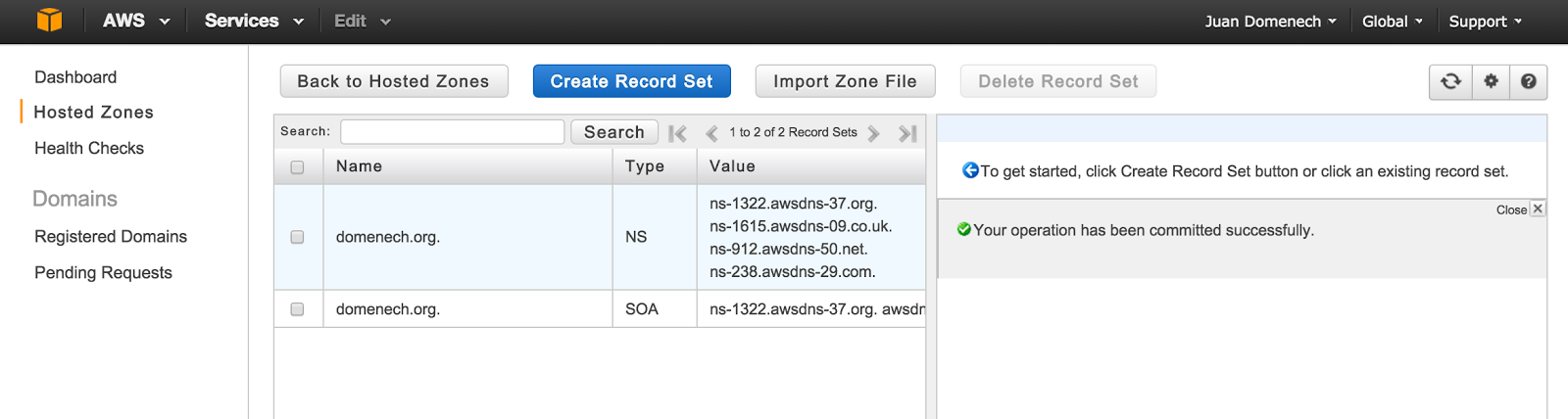
1- Create Hosted Zone
- On the Route 53 Console, click on "Create Hosted Zone" button.
- Enter your domain name (domenech.org in this example) and press "Create" button.
After a successful creation, the Zone Details will appear on screen and also the Name Servers for our domain. They will play an important role later on.
2- Obtain Zone File
- Importing a zone using API is for advanced users and is suggested for big DNS configurations. There are some tools out there to facilitate this task (Official documentation).
- Importing a zone manually using Route 53 Console is easy but only for small DNS configurations.
- Importing a zone using "Import Zone File" option on the Route 53 console is easy but relies on our ability to obtain the list of your current DNS server configuration.
Import Zone File is the method we are going to use in this example. It ensures that no typos are introduced in the migration process and is a easy repeatable method.
Here below my DNS server configuration obtained from my current ISP using a Plesk Control Panel. There are all sorts of Control Panels and Service Providers. I suggest you to send a support request to your current ISP to get that information.
Zone file:
| $ORIGIN domenech.org.
$TTL 1h
*.webmail.domenech.org. CNAME mail.domenech.org.
blog.domenech.org. CNAME ghs.google.com.
domenech.org. A 46.17.142.13
domenech.org. MX (10) mail.domenech.org.
domenech.org. MX (20) relay.celingest.es.
domenech.org. TXT v=spf1 include:celingest.es a mx ~all
ftp.domenech.org. CNAME domenech.org.
imap.domenech.org. CNAME mail.domenech.org.
ipv4.domenech.org. CNAME domenech-1821931935.us-east-1.elb.amazonaws.com.
ipv6.domenech.org. CNAME dualstack.domenech-1821931935.us-east-1.elb.amazonaws.com.
mail.domenech.org. A 46.17.142.13
pop.domenech.org. CNAME mail.domenech.org.
pop3.domenech.org. CNAME mail.domenech.org.
smtp.domenech.org. CNAME mail.domenech.org.
webmail.domenech.org. CNAME mail.domenech.org.
www.domenech.org. CNAME domenech.org.
|
The file format is simple: Three columns with DNS entry name + entry type + values separated by spaces.
Notice the two special fields at the beginning of the list: $ORIGIN and $TTL. I had to introduce them manually.
$ORIGIN is our Internet Domain Name followed by "."
$TTL 1h is the default TTL we plan to use for each entry. You can easily change that value later for individual entries using the console where necessary.
No SOA or NS records: They have to be deleted from our list. They are already present in the Hosted Zone configuration.
3- Import Zone File
- Select the newly created Zone and click on "Go to Records Sets" button.
- Click on "Import Zone File" button and Paste the contents of your Zone File.
- Press "Import" button.
You will get a successful message after a couple of seconds. Otherwise, the console will tell you what was the error and on which line number was produced.
3- Test
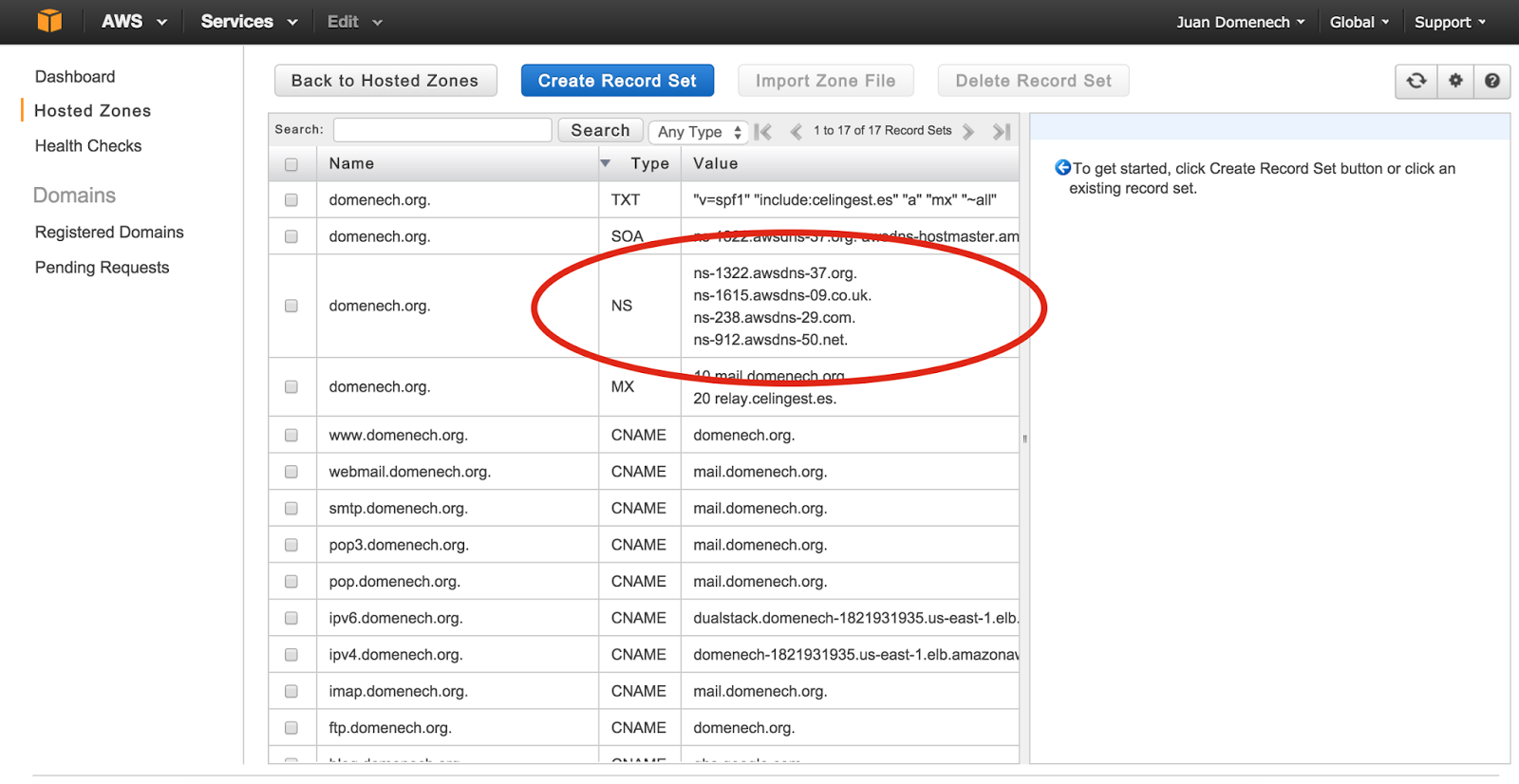
The new Hosted Zone and their DNS entries are ready to use.
This is a concept that could be difficult to wrap our head around it: Route 53 is replicating all those changes in realtime across our DNS servers and this configuration is ready to use by anyone.
But, we haven't changed our Internet Domain configuration and therefore no one is connecting to our new DNS servers. That gives us a chance to properly test the transfer result before going Live.
Where are my new DNS servers?
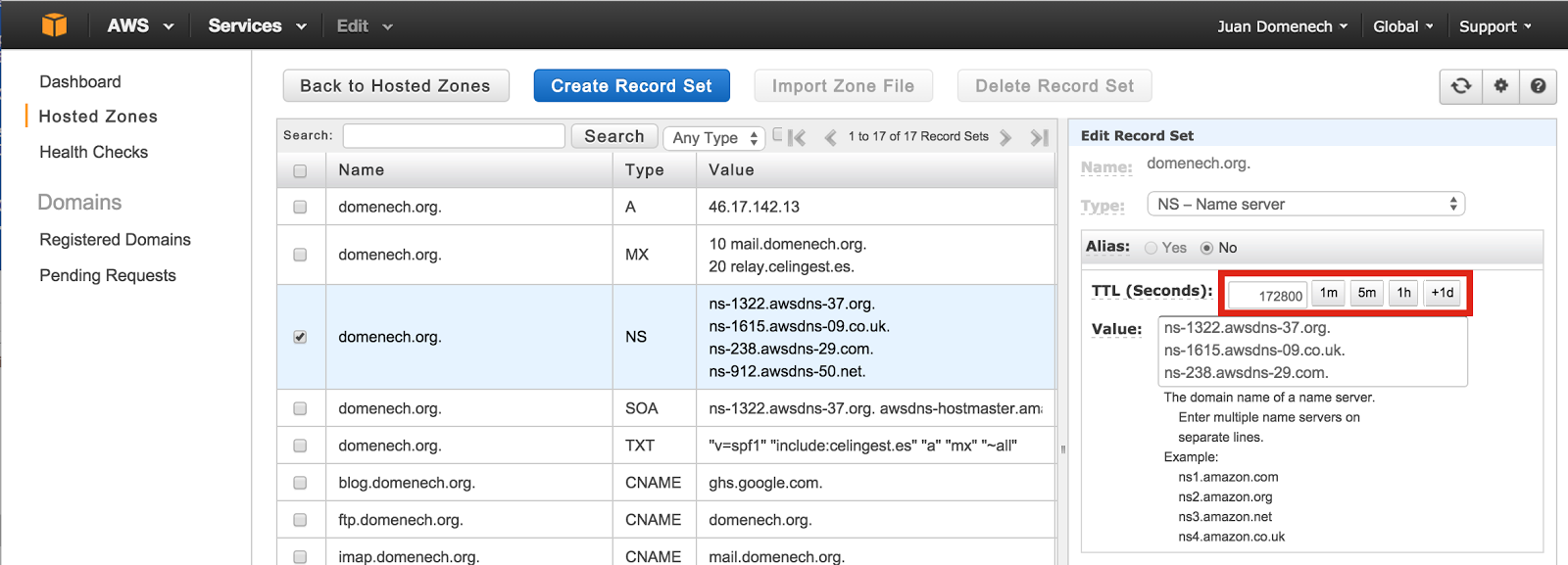
Open your Hosted Zone using Route 53 console. Your new DNS servers for are under the Type: NS.
Use dig command to query your "old" and your "new" DNS servers and compare the result.
First, lets send the request to Internet to get our current Live configuration:
$ dig mail.domenech.org
; <<>> DiG 9.8.3-P1 <<>> mail.domenech.org
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 46712
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;mail.domenech.org. IN A
;; ANSWER SECTION:
mail.domenech.org. 59 IN A 46.17.142.13
|
In this example the DNS query was "mail.domenech.org" and the answer is IP 46.17.142.13
Next we perform the same query but this time we instruct dig to ask only to one of our new DNS servers (previously obtained from the Console):
$ dig mail.domenech.org @ns-1322.awsdns-37.org
; <<>> DiG 9.8.3-P1 <<>> mail.domenech.org @ns-1322.awsdns-37.org
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 64064
;; flags: qr aa rd; QUERY: 1, ANSWER: 1, AUTHORITY: 4, ADDITIONAL: 0
;; WARNING: recursion requested but not available
;; QUESTION SECTION:
;mail.domenech.org. IN A
;; ANSWER SECTION:
mail.domenech.org. 3600 IN A 46.17.142.13
;; AUTHORITY SECTION:
domenech.org. 172800 IN NS ns-1322.awsdns-37.org.
domenech.org. 172800 IN NS ns-1615.awsdns-09.co.uk.
domenech.org. 172800 IN NS ns-238.awsdns-29.com.
domenech.org. 172800 IN NS ns-912.awsdns-50.net.
|
The answer is a bit different but the key value, the IP address, is the same. That indicates that this DNS entry has been successfully transferred.
Also notice that the TTL is 59 seconds in the first query and 3600 seconds (1h) in the second query. That is because we have specified $TTL 1h in our Zone File and all the imported entries in Route 53 have this default value. You could change it on each entry manually using the Console or repeat the import process again with a different default TTL value.
4- Rollback plan before changing Live configuration
On the next step we will change our Internet Domain DNS configuration and tell Internet to use our new DNS servers. Before doing that it is suggested to lower our NS entry TTL to 1 hour.
- Access to your Hosted Zone, select the NS entry for your domain and click on the 1h Hour button (the value will be translated to 3600 seconds) and click on "Save Record Set" button.
This instructs other DNS servers connecting to ours to come back an hour later in order to find out if the Route 53 DNS servers are still valid. This give us the option to undo this configuration in the case something goes wrong. In the worst case scenario, the issue will last an hour (the TTL value).
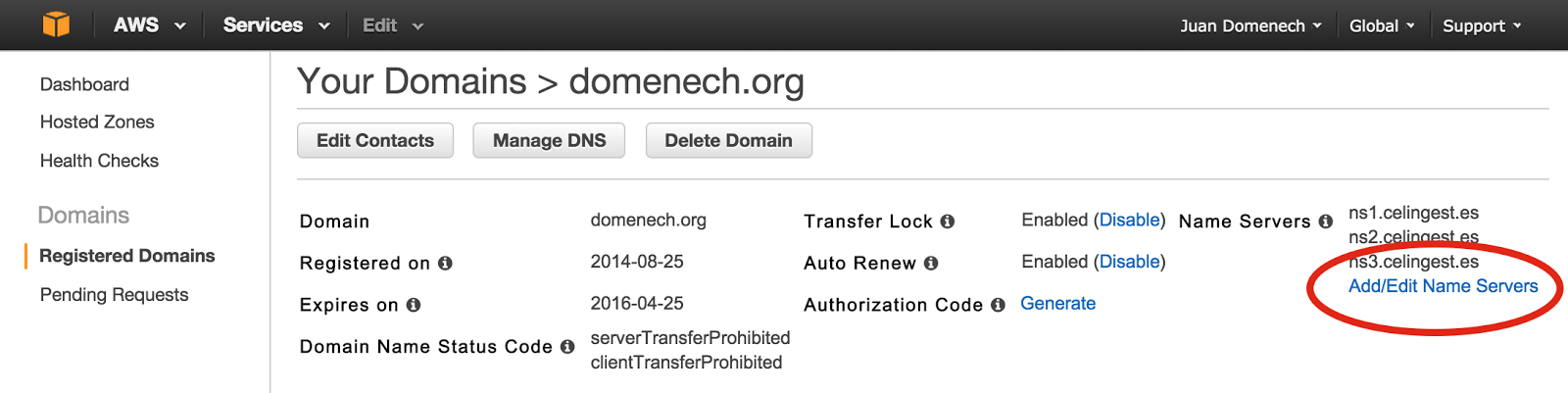
5- Change Internet Domain configuration and bring Route 53 Live
This is the step where all the previous configuration is set in motion.
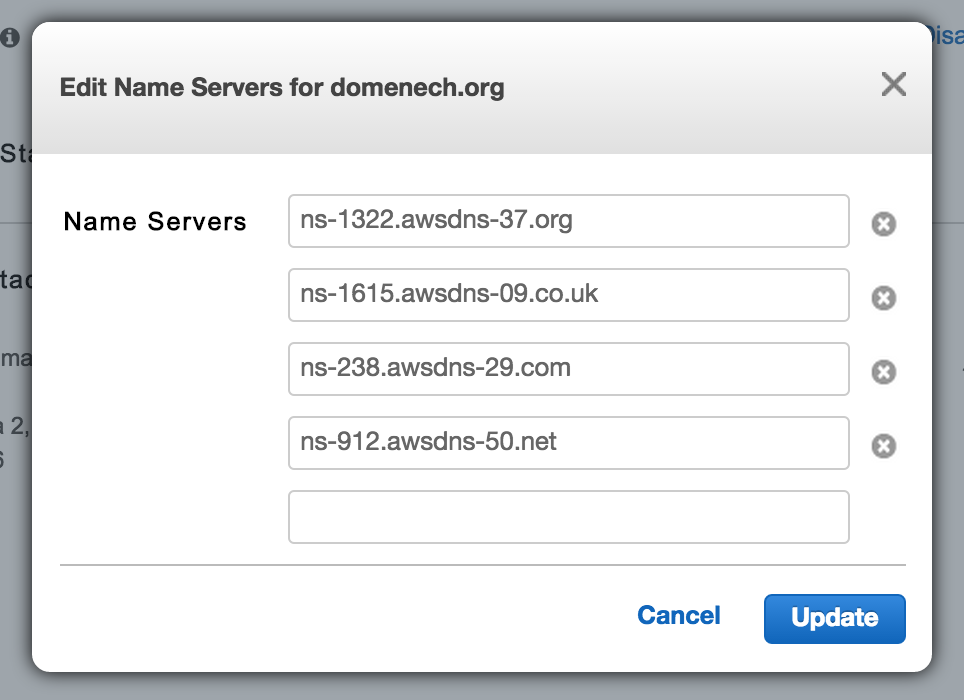
- Access to Route 53 Registered Domains, select the Internet Domain we plan to modify and click on "Add/Edit Name Servers".
- Write down the current DNS servers list in order to rollback this change if necessary.
- Introduce your new DNS servers obtained on step #3 (These shown here below are and example. Your servers names will probably differ) and click on the "Update" button.
A couple of minutes later (depending on the TTL set up on your former DNS servers) the change can be tested using dig.
$ dig domenech.org NS
; <<>> DiG 9.8.3-P1 <<>> domenech.org NS
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 29759
;; flags: qr rd ra; QUERY: 1, ANSWER: 4, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;domenech.org. IN NS
;; ANSWER SECTION:
domenech.org. 3600 IN NS ns-1615.awsdns-09.co.uk.
domenech.org. 3600 IN NS ns-912.awsdns-50.net.
domenech.org. 3600 IN NS ns-1322.awsdns-37.org.
domenech.org. 3600 IN NS ns-238.awsdns-29.com.
|
The new Route 53 servers are there and being used by anyone connection to our Internet Domain.
6- Post configuration tasks
Once we are happy and with everything tested we could bring up the TTL values. A higher TTL will improve our users experience and reduce Route 53 cost.
- Access to the NS entry and click twice on the "1d button" to select 172800 seconds (2 days).
7- Rollback
In case something went wrong we could set our former DNS servers in the Internet Domain configuration. Repeat step #5 but this time select your old DNS server list. This will bring your DNS configuration to the initial point once the TTL expires (1 hour in this example).